Ransomware becoming dangerous with double encrypting users data
By MYBRANDBOOK

Ransomware groups have always taken a more-is-more approach. Double-encryption attacks have happened before, usually stemming from two separate ransomware gangs compromising the same victim at the same time. But antivirus company Emsisoft says it is aware of dozens of incidents in which the same actor or group intentionally layers two types of ransomware on top of each other.
Emsisoft threat analyst Brett Callow, says, “The groups are constantly trying to work out which strategies are best, which net them the most money for the least amount of effort. So in this approach you have a single actor deploying two types of ransomware. The victim decrypts their data and discovers it’s not actually decrypted at all.”
Some victims get two ransom notes at once, Callow says, meaning that the hackers want their victims to know about the double-encryption attack. In other cases, though, victims only see one ransom note and only find out about the second layer of encryption after they've paid to eliminate the first.
Emsisoft has identified two distinct tactics. In the first, hackers encrypt data with ransomware A and then re-encrypt that data with ransomware B. The other path involves what Emsisoft calls a “side-by-side encryption” attack, in which attacks encrypt some of an organization's systems with ransomware A and others with ransomware B. In that case, data is only encrypted once, but a victim would need both decryption keys to unlock everything. The researchers also note that in this side-by-side scenario, attackers take steps to make the two distinct strains of ransomware look as similar as possible, so it's more difficult for incident responders to sort out what's going on.
Ransomware gangs often operate on a revenue-sharing model, where one group builds and maintains a strain of ransomware and then rents its attack infrastructure to “affiliates” who carry out specific attacks. Callow says that double encryption fits into this model by allowing clients who want to launch attacks to negotiate splits with two gangs that can each provide a distinct strain of malware.
The question of whether to pay digital ransoms is a thorny and important one. And ransomware victims who choose to pay already need to be wary of the possibility that attackers won't actually supply a decryption key. But the rise of double encryption as a strategy raises the additional risk that a victim could pay, decrypt their files once, and then discover that they need to pay again for the second key. As a result, the threat of double encryption makes the ability to restore from backups more crucial than ever.


Legal Battle Over IT Act Intensifies Amid Musk’s India Plans
The outcome of the legal dispute between X Corp and the Indian government c...

Wipro inks 10-year deal with Phoenix Group's ReAssure UK worth
The agreement, executed through Wipro and its 100% subsidiary,...

Centre announces that DPDP Rules nearing Finalisation by April
The government seeks to refine the rules for robust data protection, ensuri...

Home Ministry cracks down on PoS agents in digital arrest scam
Digital arrest scams are a growing cybercrime where victims are coerced or ...


Icons Of India : NIKHIL RATHI
Co-founder & CEO of Web Werks, a global leader in Data Centers and Clo...

Icons Of India : NANDAN NILEKANI
Nandan Nilekani is the Co-Founder and Chairman of Infosys Technologies...

Icons Of India : MADHABI PURI BUCH
Madhabi Puri Buch is the first-female chairperson of India’s markets...


GSTN - Goods and Services Tax Network
GSTN provides shared IT infrastructure and service to both central and...

STPI - Software Technology Parks of India
STPI promotes and facilitates the growth of the IT and ITES industry i...

UIDAI - Unique Identification Authority of India
UIDAI and the Aadhaar system represent a significant milestone in Indi...

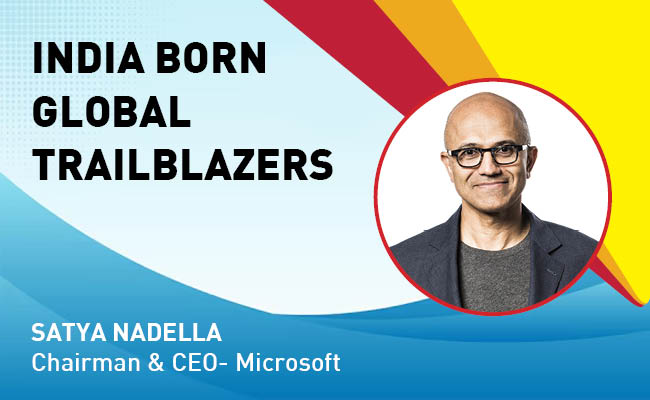
Indian Tech Talent Excelling The Tech World - Satya Nadella, Chairman & CEO- Microsoft
Satya Nadella, the Chairman and CEO of Microsoft, recently emphasized ...

Indian Tech Talent Excelling The Tech World - Vinod Dham, Founder & Executive Managing Partner, IndoUS Venture Partners
Vinod Dham, known as the “Father of the Pentium Chip,” has left an...
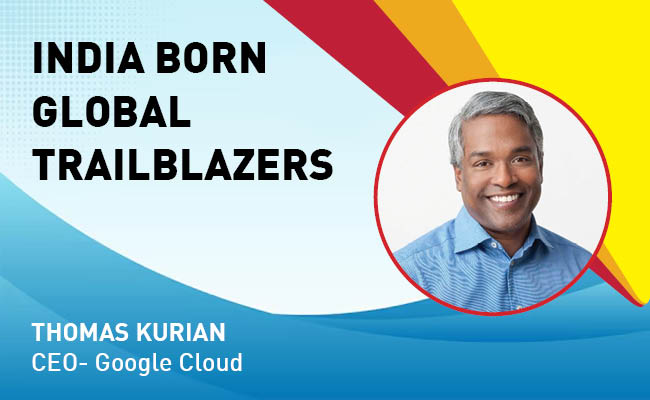
Indian Tech Talent Excelling The Tech World - Thomas Kurian, CEO- Google Cloud
Thomas Kurian, the CEO of Google Cloud, has been instrumental in expan...
 of images belongs to the respective copyright holders
of images belongs to the respective copyright holders